Quantum Computing Heros
A Play In Three Acts
Is This Real? or Here’s The Thing
You wake up tomorrow to the headlines that a physicist broke an important encryption cipher using quantum computing. “Chinese scientists hack encryption in quantum computer experiment,” screams the headline.
Look, there is no doubt that quantum computing will change the future of many things, including encryption. And it’s easy to buy into the immediacy of some post-quantum cryptography/encryption (PQC/E) storylines. After all, cybersecurity professionals have a duty and desire to protect.
So, should we continue as usual or buy tickets to this show?
Plot Twist or PQC PDQ?
Imagine a world where you couldn’t trust a bank to keep your money safe. We rely on encryption to keep important information confidential and secure.
In other words, encryption is a means of online trust. It works as a means of trust because it’s tough to decipher encrypted data using classical computing. But in a Martin McDonagh-esque plot twist, society doesn’t work as it’s currently configured without it.
Of course, there's trouble brewing, just like any good theatrical plot. A new threat is on the horizon, and its name is PQC. And finally, at long last, cybersecurity pros are cast as heroes!
We need heroes to the ready pretty damn quick (PDQ)! Ok, actually…wait a second. Let’s set the stage by thinking more about the PQC headline hype and getting the backstory on the set and cast of characters.
Backstory or How Do Classical Encryption Standards Keep Information Safe?
Quantum computers are a new type of technology being developed by larger companies and many countries that will provide unprecedented computing power, eventually dwarfing the capabilities of today’s classical computers. The future of quantum computing’s ability to power exciting advances in fields like AI, medicine, and science is unimaginable and undeniable. At the same time, this tremendous computing power could one day also be used to break present-day encryption.
Quantum computing is a breakthrough technology because it can read and process massive amounts of data more efficiently than classical computers.
Today’s computers process data using bits, essentially electrical or optical on/off impulses representing 0s and 1s. On the other hand, a quantum computer harnesses the mystical properties of quantum mechanics to provide a giant leap forward in processing power.
The reason quantum computing is so powerful is because of something called superposition. This means that a quantum computer using qubits (quantum bits) can represent both 0 and 1 simultaneously. When you have multiple qubits, they can represent many combinations all at once.
Here's a simple analogy. Say you have two classical computing bits. Those 2 bits can represent 4 possible combinations (00, 01,10, and 11), but only one combination at a time. With 2 qubits, however, you can represent all 4 combinations simultaneously. Since qubits can handle multiple states simultaneously, a quantum computer can read or process massive amounts of data (or potential outcomes). This means it can solve complex problems much faster than a classical computer.
You can tour Encryptionville for an overview of the basics, but essentially, modern encryption uses algorithms like RSA (Rivest-Shamir-Adleman) and ECC (Elliptic Curve Cryptography) to keep information secure. These encryption methods rely on the difficulty of factoring large numbers (RSA) or solving the discrete logarithm problem (ECC), which is infeasible for classical computers to solve efficiently.
Several core types of cryptography keep our information secure. First, we have symmetric key cryptography (SKC), which is used for fast data encryption. In SKC, the sender and receiver share a single secret key for encrypting and decrypting data. Symmetric encryption protects stored data (“data at rest”) and data transmitted over networks (“data in transit”). SKC is known for its speed and efficiency but requires secure key distribution and management.
The second type of cryptography is public key cryptography (PKC). PKC is used for secure communications where parties do not share a secret key beforehand. Public-key cryptography uses a two-key system consisting of the public and the private keys, where messages are encrypted with one key and decrypted with the other. The first time symmetric key cryptography is used, PKC creates a shared key. This secure way of exchanging symmetric keys is the province of algorithms such as Diffie-Hellman (DH) and RSA.
Two components are required to make PKC work with SKC. The first is key establishment. For example, if you go to a bank’s website for the first time, you need to be able to communicate with the bank securely using a shared secret. But how do you exchange that information without someone being able to intercept it? The technical name for this process is key encapsulation, the technique used to securely exchange a symmetric key over an insecure channel using PKC.
You start by encrypting (or encapsulating) the symmetric key with the recipient’s public key so only they can decrypt and retrieve it (using their private key). Algorithms like RSA and Elliptical Curve Integrated Encryption Scheme (ECIES) are used for key encapsulation, and DH and Elliptical Curve Diffie-Hellman (ECDH) are used for key establishment.
PKC is also used with digital signatures, verifying the authenticity and integrity of a message or document, ensuring it was sent by the claimed sender and hasn't been unknowingly modified. Algorithms like RSA and ECDSA (Elliptic Curve Digital Signature Algorithm) are widely used for creating and verifying digital signatures.
This process is used when doing things like updating software on your computer. If you update an app from the app store, your computer or phone tries to ensure that the download is legit, came from the correct source, and doesn’t contain anything harmful. To do this, the download contains a digital signature that is used to verify the update’s authenticity.
Que the Mathematician or How Does Quantum Computing Threaten Classical Encryption Standards?
In 1994, a mathematician named Peter Shor created an algorithm that promised a “quantum leap,” reducing the time it takes to factor integers and find discrete logarithms, enabling a quantum computer to crack most of the currently used public key cryptosystems.
This means that some encryption used today will be vulnerable to quantum computing. With this in mind, if you re-read those headlines, you likely think we are all doomed. The villains are about to win. But hold on a moment.
The Shor implementation has a few caveats when used to break current encryption. First, because Shor’s algorithm applies to factoring large integers and solving the discrete logarithm problem, it is primarily a threat to RSA, ECC, and DH cryptosystems. Unlike RSA and its asymmetric siblings, symmetric encryption is widely believed to be safe from quantum computing as long as bit sizes are “large enough”.
A Play In Three Acts or The Case For Some Calm
Being in IT and cybersecurity for decades tends to shape your reflexes. As an IT/security leader, you are the designated defender, often on the cutting edge of technology. The C-suite has its own focus and agendas, and it’s up to you to help influence an organization toward secure strategy and processes.
There are a lot of technical issues with the article cited above (ArsTechnica does a good job debunking claims). But China is challenging US quantum leadership, and it’s always difficult to accurately estimate the timing and path of advancement.
While we will not panic, there is cause for concern if we consider the opening act to be the race to create a quantum machine powerful enough to threaten classical asymmetric cryptography and the general recognition of the problem.
Harvest Now, Decrypt Later (HNDL) is the threat of adversarial interception and storing encrypted data, with the intent of using quantum computers to decrypt it in the future. HNDL is the second act of this play and is a problem for any business with proprietary interests that extend beyond the next few years.
The final act will be the availability of a quantum machine capable of breaking current classical encryption. Before this third act begins, we must have rolled out and implemented quantum-resistant algorithms.
What Action Steps Should We Take or Where Do We Get Tickets To This Production?
NIST has led an initiative to develop and standardize secure cryptographic algorithms against the threats posed by quantum computers. In 2016, NIST announced a global call for proposals to develop quantum-resistant public-key cryptographic algorithms. The goal was to find algorithms that could replace current standards like RSA and ECC.
In July 2022, NIST announced the first set of algorithms selected for standardization. In August of this year, NIST requested comments on the initial public drafts of three Federal Information Processing Standards (FIPS). These proposed standards specify key establishment and digital signature schemes designed to resist future quantum computer attacks. The three algorithms specified in these standards are derived from different NIST PQC Standardization Project submissions.
Quantum-resistant cryptography aims to develop secure cryptographic systems against quantum and classical computers that can interoperate with existing communications protocols and networks.
It’s time for every organization to start a program incorporating PQC-safe security algorithms. Forward-thinking companies like Cloudflare and Google are already implementing post-quantum cryptography.
Chrome began supporting X25519Kyber768 for establishing symmetric secrets in TLS, starting in Chrome 116. This hybrid mechanism combines the output of two cryptographic algorithms to create the session key used to encrypt the bulk of the TLS connection:
X25519 – an elliptic curve algorithm widely used for key agreement in TLS today
Kyber-768 – a quantum-resistant Key Encapsulation Method and NIST’s PQC winner for general encryption
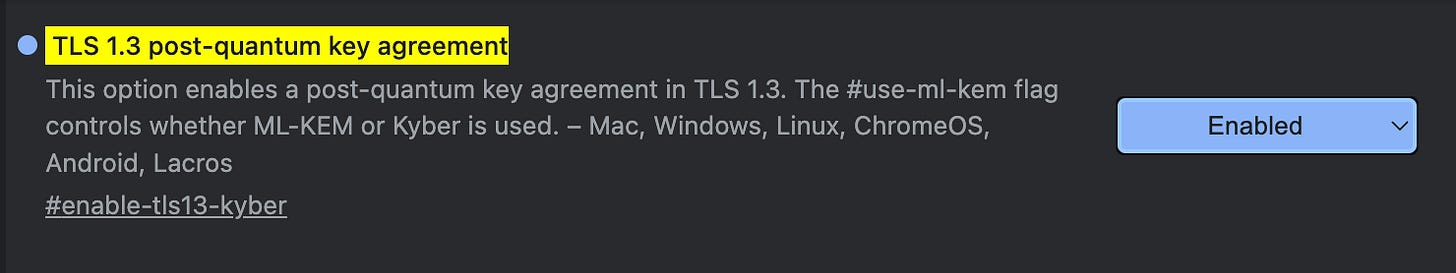
You can enable Kyber support if you use Chrome. If your Google Chrome browser runs version 116 or later, you can enable Kyber support as follows: simply open your browser and enter the following in the address bar: chrome://flags/#enable-tls13-kyber and change the associated dropdown from Default to Enabled.
Another example is Cloudflare, using X25519Kyber768 to secure their site — see the image below.
Quantum computing advancements are happening fast. As far as we know, there hasn’t been a quantum machine that has stabilized enough qubits to threaten current asymmetric algorithms.
However, incorporating new standards takes a lot of time, and with HDNL, the time to start is now.
Curtain Call or TL;DR
This play ends well if we start moving forward now. Even if quantum computing isn’t advanced far enough to break public key encryption today, SNDL is a growing threat to future confidentiality.
Quantum computing poses both a threat and an opportunity. You can be a part of the solution by adopting quantum-resistant encryption, updating infrastructure, and staying informed about quantum developments.
Here’s hoping you break a leg in your efforts!
I’m an IT and information security leader with over two decades of IT executive leadership and cybersecurity experience in multiple industries. If you enjoyed this article, consider subscribing to my blog, where I write about cybersecurity, and connect with me on LinkedIn. If you’re studying for the CISSP exam, look at my study resources on Git Hub, and reach out if you have questions. We can learn together! Thank you for reading.