Keeping Up with the NIST CyberSecurity Framework
Kickflipping the gaps like no other framework
Introduction
The tech world faces many cybersecurity challenges. Continuously evolving ransomware, cloud service misconfigurations, supply chain attacks, changing compliance, exploding BYOD and IoT — and the list is growing. Best practices, understanding threats, and having a common way of communicating around cybersecurity should empower and unite defenders, not be part of the challenge. Unfortunately, there has been a dearth of standard rules, language, and approaches for dealing with this significant area of business risk.
The National Institute of Standards and Technology (NIST) CyberSecurity Framework (CSF) is a potential lingua franca that helps bridge this gap. The CSF is a voluntary set of standards, guidelines, best practices, and recommendations that empower organizations to improve their cybersecurity posture. The CSF provides a common language and a structure to ease the governing process of identifying, protecting, detecting, responding, and recovering from cyber threats.
You may be thinking, “How can a NIST security framework keep up with the rapid pace of technology?” But don’t be worried; CSF is the Ryan Sheckler of technology vehicles — flexible and adaptable, ollieing and kickflipping its way through the knowledge, language, and standards gaps — users can customize the Framework to their implementation based on specific needs and context.
You may also think, “CSF, where have you been all my life?” But don’t be fooled; the CSF has been getting around. Adopted by various industries and countries and widely praised, it helps improve cybersecurity posture and resilience, comply with regulations and standards, and communicate progress and challenges to organizational stakeholders. The CSF fosters collaboration and innovation among different sectors and communities, creating a more secure and trustworthy cyberspace.
NIST is updating the CSF to keep pace with the evolving cybersecurity landscape. The version 2.0 draft, released in August 2023, introduces more significant changes and enhancements, such as a new GOVERN function and implementation examples, metrics, and governance models. CSF 2.0 aims to provide more guidance and value to the users of the Framework and address the emerging challenges and opportunities in cybersecurity.
Let's explore the CSF and the need for corporate leaders to understand it and get ready to adopt version 2 to strengthen their organization's cybersecurity posture.
Background of NIST CyberSecurity Framework
In 2013, the Obama administration issued Executive Order 13636, which tasked NIST with creating a framework to reduce cyber risks to critical infrastructure. The following year, the Cybersecurity Enhancement Act of 2014 mandated that NIST develop and maintain a voluntary, consensus-based, industry-led set of standards, guidelines, best practices, methodologies, procedures, and processes for cost-effective cybersecurity. NIST released the CyberSecurity Framework version 1.0 in 2014, adding additional updates in version 1.1 in 2018.
Since then, NIST has incorporated the feedback and input from various stakeholders, including small businesses (as per the NIST Small Business Cybersecurity Act) and higher education institutions (as per the CHIPS and Science Act), into the Framework. You might say that CSF is the graphene of cybersecurity risk toolsets designed to be applicable and adaptable to any organization regardless of size, sector, or maturity. NIST is also providing additional resources to support the implementation of the Framework, such as the updated NIST SP 1271 quick start guide (Getting Started with the NIST Cybersecurity Framework: A Quick Start Guide).
Key Changes in NIST CSF Version 2.0
CSF 2.0 is the latest version of the voluntary set of guidelines and best practices for managing cybersecurity risks in different organizations and sectors, introducing several major changes and enhancements compared to the previous version 1.1:
CSF has an expanded scope covering critical infrastructure and any organization that uses or provides digital products or services.
It adds a new GOVERN function focused on cybersecurity's strategic and organizational aspects, also known as GRC (governance, risk management, and compliance).
Expands guidance on cybersecurity supply chain risk management, an area of growing risk to many companies.
It provides additional guidance on measuring cybersecurity outcomes and integrates cybersecurity risk management into broader organizational risk management.
CSF 2.0 includes improved and expanded guidance on implementation, including the development of profiles. Profiles are the Framework's mechanism for describing an organization's current or target cybersecurity posture. Since the Framework is adaptable to organizations with cybersecurity programs at different stages of maturity, the idea is for an organization to create a current-state snapshot or profile and one for the target state. These profiles allow businesses to perform a gap analysis, estimate costs, prioritize tasks, and create an action plan to improve their cybersecurity posture.
The latest version of the Framework describes CSF alignment with newer NIST guidance like the Privacy Framework, reflecting lessons organizations have learned after living with and using it.
Finally, it provides more implementation examples, metrics, and governance models, illustrating how the CSF can be applied and measured in different scenarios and contexts.
Focusing on international collaboration and information exchanges, CSF 2.0 will provide guidelines for standardized, compelling, and adaptable risk management worldwide. NIST seeks information on translations, adaptations, and resources for CSF to enable international engagement.
Overall, CSF 2.0 aims to provide more guidance and value to the users of the Framework and address the emerging challenges and opportunities in cybersecurity.
Enhanced Focus on Emerging Threats and Technologies
Let's break down the critical elements of NIST CSF 2.0, exploring the Framework Core and its expanded scope, changes to Core functions, introducing the GOVERN function, and including guidance around profiles.
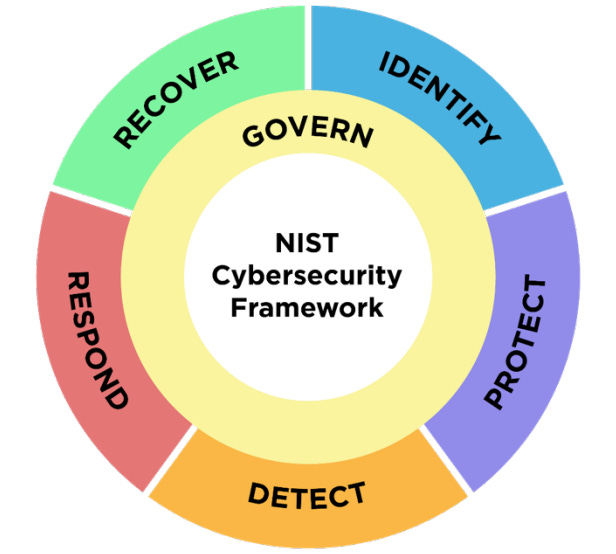
The Core provides a set of security outcomes, examples of how to achieve these outcomes, and references to additional guidance. The Framework's Core Functions — GOVERN, IDENTIFY, PROTECT, DETECT, RESPOND, and RECOVER — organize cybersecurity outcomes at their highest level.
Here is an overview of the GOVERN Function, including its purpose, role, and critical activities:
Purpose: Establish and oversee the organization's cybersecurity risk management strategy.
Cross-Cutting Role: Informs how the organization achieves and prioritizes outcomes across the other five CSF functions.
Critical Activities:
Contextual Understanding: Provide practitioners and stakeholders with the circumstances — mission, stakeholder expectations, and legal, regulatory, and contractual requirements — surrounding and affecting the organization’s cybersecurity risk management decisions.
Strategy Establishment: Development of a robust cybersecurity strategy informed from risk management and performance.
Supply Chain Risk Management: Address cybersecurity risks in the supply chain.
C-SCRM Importance: CSF 2.0 underscores the critical role of C-SCRM in identifying and mitigating risks inherent in distributed supply chains. The main goal of C-SCRM is to apply proper cybersecurity risk management practices, initially focused on the organization itself, to third parties, supply chains, and the products and services an organization purchases, depending on the criticality and risk assessment of the suppliers.
Hygiene Priority: Cybersecurity hygiene becomes mission-critical for C-SCRM.
Vulnerability Mitigation: C-SCRM investigates technology, hardware, open-source, and proprietary software vulnerabilities.
Key Considerations:
Supply Chain Awareness: Understand item origins, company location, foreign involvement, legal issues, and past breaches.
Continuous Monitoring: Vigilantly monitor vendor relations.
Avoid Assumptions: Past purchases from the same supplier may still pose risks.
Key issue: The challenge with C-SCRM is summed up in this sentence (from GV.SC-07): “The risks posed by a supplier, their products and services, and other third parties are identified, recorded, prioritized, assessed, responded to, and monitored over the course of the relationship.” I agree; identifying and assessing third-party supplier risks is essential if it were only that easy.
Roles and Responsibilities: Define clear roles and authorities. NIST notes that adequate resources should be commensurate with the cybersecurity risk strategy.
Policy and Procedure Oversight: Ensure adherence to policies and processes.
GOVERN ensures that cybersecurity aligns seamlessly with the broader enterprise risk management strategy, weaving resilience and informed decision-making into the organization's fabric.
The essence of the IDENTIFY (ID) Function:
Purpose: Determine the current cybersecurity risk to the organization.
Asset Understanding: Inventory assets (data, hardware, software, systems, facilities, services, people) and their associated cybersecurity risks.
Prioritization: Prioritize efforts aligned with risk management strategy and mission needs.
Improvement: Identify enhancements for policies, processes, procedures, and practices supporting cybersecurity risk management across all six functions.
IDENTIFY lays the groundwork for informed risk mitigation and strategic alignment in the dynamic cybersecurity landscape.
The updated CSF 2.0 components previously grouped under IDENTIFY have significantly changed. Many of these components have been divided or moved to the new GOVERN function, apparent in the "Oversight" category, highlighting the Framework's increased focus on governance principles. This strategic realignment involves policies, procedures, security, and internal practices to ensure smooth operation.
Combining these elements into one function helps improve transparency and accountability. The "Oversight" feature ensures the Framework aligns more closely with regulatory requirements, such as those from the SEC, which underscore the responsibilities of the Board of Directors and senior management. This focus highlights the leadership team’s crucial role in making important IT security decisions.
The PROTECT (PR) Function can be summarized as follows:
Purpose: Employ safeguards to prevent or mitigate cybersecurity risk.
Asset Security: PROTECT heightens security to minimize adverse cybersecurity events against identified assets.
Key Outcomes:
Awareness and Training: Educate personnel with user awareness and security training practices.
Data Security: Safeguard sensitive information, such as the confidentiality, integrity, and availability of data at rest and in transit.
Identity Management and Access Control: Ensure users, services, and hardware are authenticated. Access permissions, entitlements and authorizations are defined in an enforced and reviewed policy.
Platform Security: Secure hardware, software, and virtual platforms.
Technology Infrastructure Resilience: Security architectures are managed in alignment with the organization’s risk strategy to protect asset confidentiality, integrity, and availability and increase organizational resilience.
In summary, PROTECT fortifies an organization's defenses, reducing the impact of cyber threats and ensuring operational continuity.
The essence of the DETECT (DE) function:
Purpose: Analyze and detect cybersecurity attacks and compromises.
Timely Discovery: DETECT promotes prompt identification of anomalies via continuous monitoring, looking for indicators of compromise, and analyzing events to detect cybersecurity incidents.
Vigilance: Enabling organizations to respond swiftly to ongoing attacks and incidents.
In summary, DETECT enhances an organization's situational awareness, allowing proactive defense against cyber threats.
The RESPOND (RS) Function within the CSF 2.0 helps organizations understand how to contain and reduce the impact of cybersecurity incidents:
Purpose: Respond to detected cybersecurity incidents.
Impact Containment: Incidents are contained and eradicated as quickly as possible to limit incident impact, and activities are coordinated with internal and external stakeholders as required by laws, regs, or policies.
Key Outcomes:
Incident Management: Efficiently handle incidents.
Analysis and Mitigation: Investigate and mitigate threats.
Reporting and Communication: Transparently communicate incident details.
In summary, RESPOND empowers organizations to address and manage cybersecurity incidents swiftly, minimizing disruption and ensuring resilience.
Finally, the RECOVER (RC) Function provides the following:
Purpose: Restore assets and operations affected by a cybersecurity incident.
Impact Mitigation: RECOVER ensures a timely return to normal operations, minimizing incident impact.
Key Outcomes:
Asset Restoration: Recover compromised assets.
Operational Resumption: Resume business functions.
Effective Communication: Enable transparent recovery efforts.
RECOVER fosters resilience by helping organizations understand and plan for rapid restoration functionality and ensuring transparent communication during recovery.
The Impact on Corporate Cybersecurity Strategies
CSF 2.0 will emphasize the importance of cybersecurity governance, which defines how to manage and control cybersecurity-related activities, and the role of leadership and the risk management function in driving effective practices. Governance provides policies, procedures, and standards to ensure a cybersecurity program aligns with an organization's mission and goals.
Key governance components that are part of these additions include:
Risk Management: Policies, procedures, and mitigations to identify, assess, and prioritize risks based on potential impacts.
Policies and Procedures: Standardize ways of addressing access control, data protection, incident response, and security awareness/training across the organization.
Organizational Structure: Help create and manage a cybersecurity program, including defined roles and relationships and an established reporting structure.
Compliance and Oversight: Mechanisms to ensure alignment with applicable laws, regulations, and standards.
Robust governance plays a significant role in safeguarding the security and resilience of organizational assets and infrastructure. By adopting a governance program aligned with CSF 2.0, organizations can proactively manage risks, adhere to regulatory requirements, and elevate their overall cybersecurity posture.
Finally, measuring and assessing the efficacy of an organization's cybersecurity plan gets more emphasis in 2.0:
Frameworks and Key Performance Indicators (KPIs): Creating the structures and selecting KPIs for measuring and evaluating cybersecurity posture have elevated importance.
Collect Accurate Data: Collecting data used to track reliability and consistency more precisely.
Conduct Regular Assessments: Emphasis on regular internal and external program assessments, which help keep abreast of changing risks.
Continuous Improvement: Prioritize and make continual improvement a core organizational focus, helping to keep the cybersecurity plan evergreen.
Best Practices: Being part of the community and sharing knowledge allows members to understand and continually improve measurement and assessment.
NIST will retain CSF's level of detail, but they have planned updates to connect to existing standards. CSF 2.0 will relate to commonly known NIST frameworks, including the RMF, referencing these as guidance.
Using the Cybersecurity and Privacy Reference Tool (CPRT), NIST highlights reference data from other publications without the constraints of PDF files. The CPRT provides better searching through reference data, standards, and tools using an online database, including exporting structured data in human- and machine-consumable formats.
CSF 2.0 will include more recently changed technology areas, including Zero Trust, Respond and Recover Functions, and Identity Management, providing organizations with additional guidance on how these areas affect cybersecurity risk.
Conclusion
The tech world faces many cybersecurity challenges, and NIST’s CyberSecurity Framework (CSF) helps organizations meet them. The CSF is a voluntary set of standards, guidelines, best practices, and recommendations that help organizations improve their cybersecurity posture.
The broad changes of CSF version 2.0 include expanding the application and scope of the Framework to cover more use areas, benefit more organizations, and encourage collaboration internationally. CSF was originally specific to critical infrastructure, and the rebranded version 2.0 will reflect its intended application across all government, industry, and academia. The new version is expected to be finalized in the first quarter of 2024. High-tail it over to NIST to get your copy!